Configuring Azure for Monitoring with the Azure Sensor Pack
- nmsguru
- Mar 26, 2023
- 2 min read
Updated: Jul 8, 2023
This article covers the procedure of how to configure your Azure cloud for monitoring with the AutoMonX Azure Sensor pack. You need to obtain three items to configure a connection profile in the Azure Sensor pack: App ID, Tenant ID and Secret Key.
Quick run through of the flow after you login into your Azure Portal:
Register an App
Assign the App ID to Subscriptions
Retrieve the App ID and Tenant ID
Retrieve the Azure Secret Key
Add special settings for monitoring Secret Keys
1. Register an App Select Azure Active Directory -> App registrations -> New registration

In the next windows:
Choose an application name (for example azure_monitor1).
Select Accounts in this organizational directory only (Single tenant)
Select Web and fill a URL (i.e. https://myapp.com/auth)
And Click Register

2. Assign the App ID to relevant Subscription(s)
Repeat the procedure below for all the subscriptions you wish to discover and monitor:
Type Subscriptions in the search box
Click the Subscriptions item in the Services window
Grant read-only permissions to the App ID as seen in the next screen

Grant permissions for accessing a subscription is shown below:
Select Access control folder (IAM)
Select Add button and select Add role assignment
Select in the Add role assignment box the role of Reader.
In the Assign Access to box the service principal option.
Fill in the select box the name of Application ID connection
Select the application id you created earlier
Click the Save button.

3. Retrieve the Application ID and Tenant ID
Go to Azure Active Directory -> App registrations -> Select the application you have registered

Copy the Application ID and Tenant ID

4. Retrieve the Azure Secret Key Navigate to Azure Active Directory -> App registrations -> Select the application.

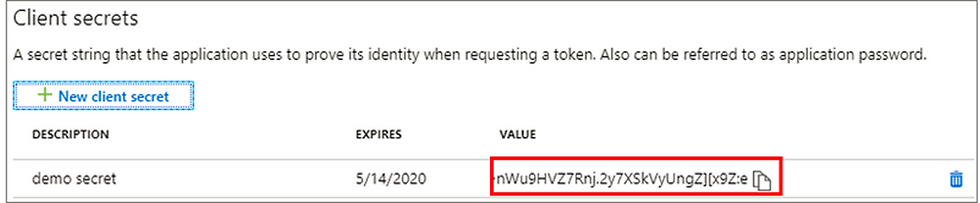
Click the Certificates & Secrets menu
Select under Client secrets the New client secret button
Fill a in the Description
Select when the token will expire. The longest expiry time is two years, this is why monitoring of it is important
Select Add

Copy the Secret Key - In the next page copy the secret key because you won’t be able to retrieve it afterwards.
5. Adding permissions for the App Secret Monitor
The App Secret monitoring requires additional permissions to run properly. The addition of permissions is done through the Azure Active Directory panel.
From the panel for each App in the App registrations panel perform the following:

Click API Permissions and click the Add a permission button. From there go to Microsoft Graph and add a permission from type Application named:
Application.Read.All
Make sure to give it Admin consent.






Comments